Remediation
Found it. Proved it. Fixed it.
Every validated API finding comes with a developer-ready fix. Vortex generates the Jira ticket, opens the pull request, and writes the remediation guidance — specific to the vulnerability class and your technology stack. Your developer fixes it. Vortex retests. Finding closed.
Step-by-step fix instructions written for the specific vulnerability class — not a link to the OWASP documentation. For an IDOR finding, Vortex explains exactly how to implement object-level authorization checks in the context of your API framework. For a broken authentication finding, it walks through the token validation logic that needs to change. Specific to your stack. Actionable immediately.
02
Automated Jira Tickets
Every confirmed API finding creates a Jira ticket automatically — vulnerability title, severity, affected endpoint, HTTP method, the payload that confirmed it, business impact, and remediation steps. The ticket includes enough context that a developer can fix the issue without needing a separate briefing from the security team. Closed automatically when Vortex confirms the fix on retest.
Auto-closed on retest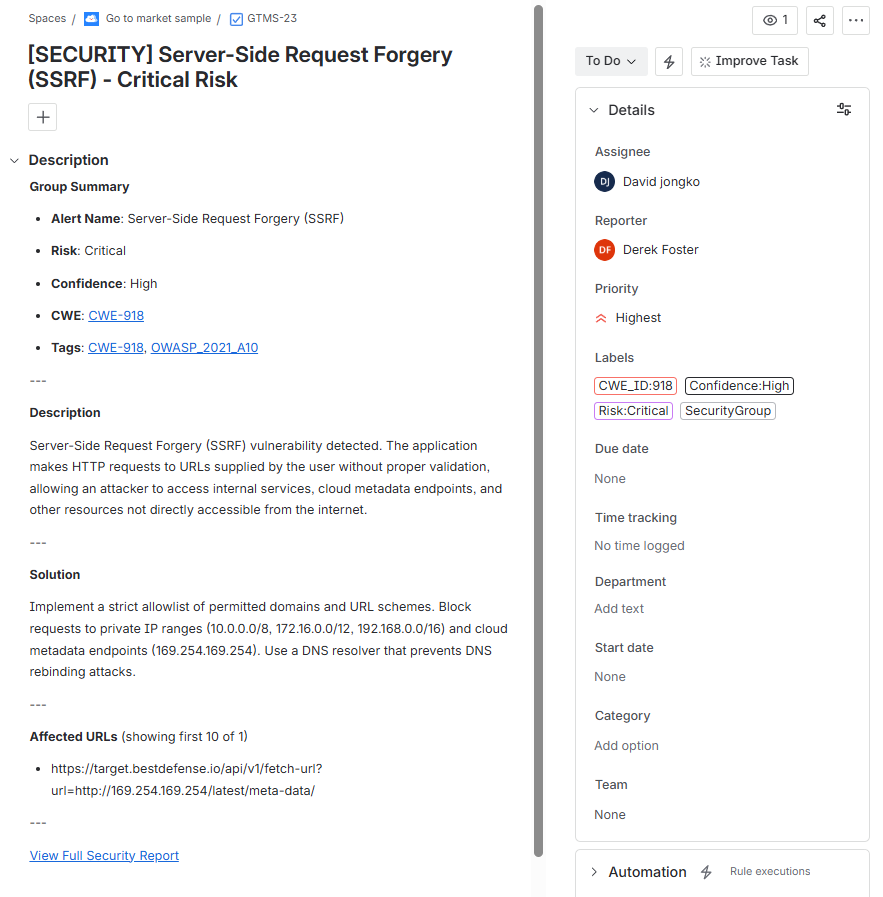
03
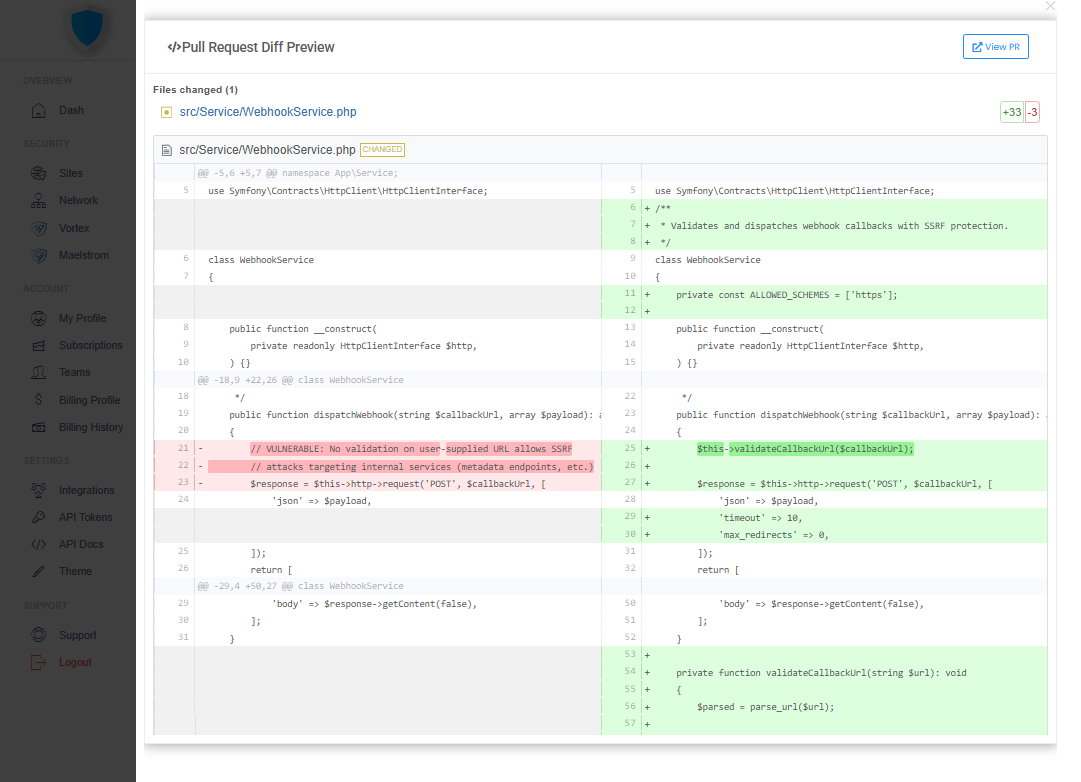
Auto-Fix Pull Requests
For common API vulnerability classes — authentication validation gaps, missing authorization checks, insecure deserialization — Vortex generates a pull request in your repository with the fix code already written. Your developer reviews the diff and merges. The vulnerability is closed. The fix is on record and linked to the finding.
GitHub · GitLab · Bitbucket