// STEP 01 — CRAWL
Know your attack surface before an attacker does.
Vortex starts where attackers start: crawling your application like a threat actor would. It discovers every exposed endpoint, unauthenticated route, API surface, auth flow, and third-party dependency. The target map rebuilds on every deploy, so your coverage never goes stale between releases.
Endpoint enumeration
API surface mapping
Auth flow analysis
Dependency graph
CI/CD config audit
Shadow API detection
Every
deploy, automatically
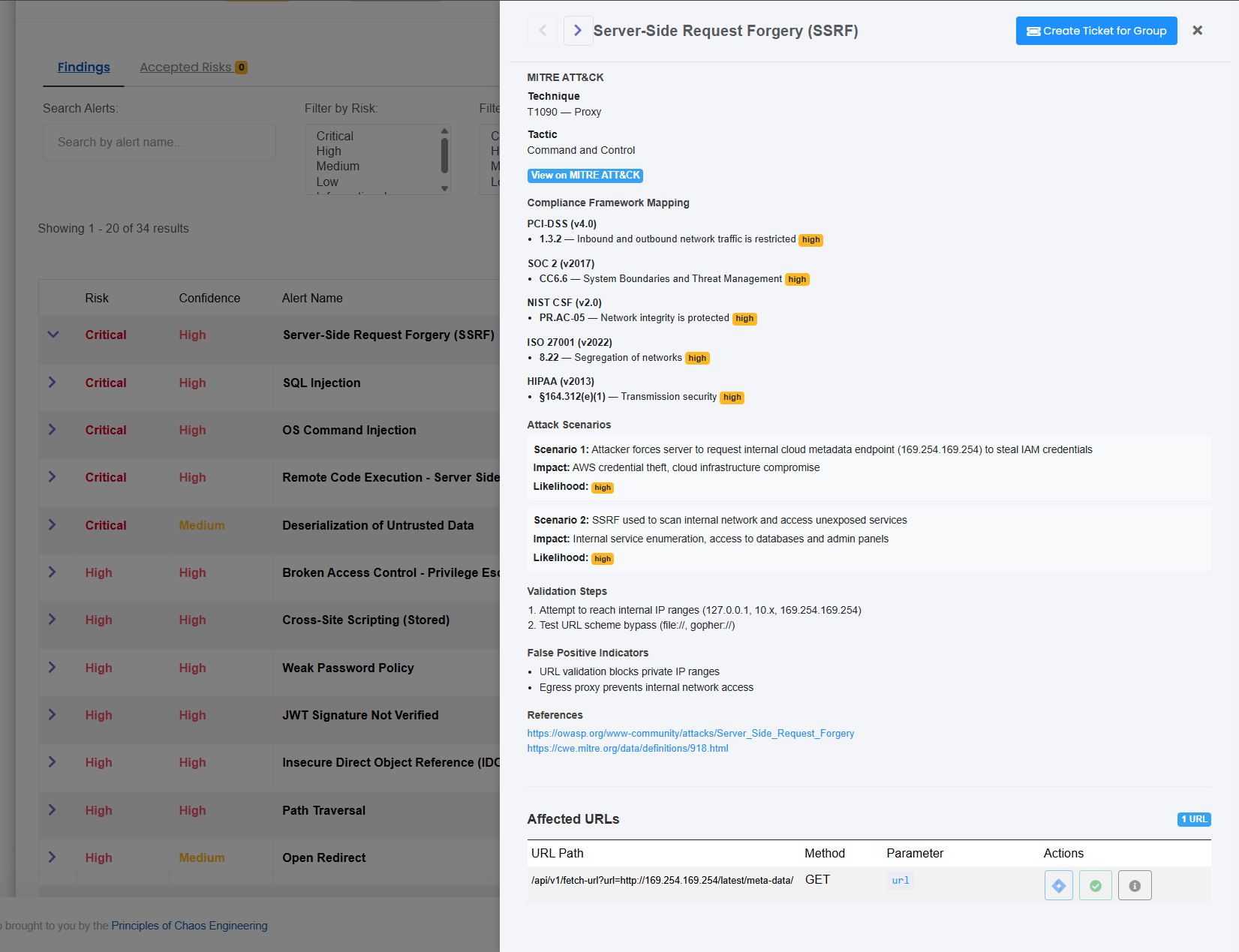
// STEP 02 — PENTEST
What used to take a team two weeks now runs in minutes.
Vortex executes the same techniques a senior pentester would: SQL injection, SSRF, privilege escalation, auth bypass, business logic flaws, prompt injection. It runs against every version of your code, not just quarterly. Every finding is confirmed via a live exploit chain against a real target. If it doesn't execute, it never reaches your team. Zero false positives isn't a feature. It's the contract.
SQL injection
Auth bypass
Privilege escalation
SSRF
Business logic flaws
Prompt injection
Every
deploy, not quarterly
// STEP 03 — FIX
A pull request, not a PDF. Nothing ships until it's clean.
For every confirmed exploit, Vortex generates a production-ready PR with the exact code change, test coverage, and full remediation context, scoped to your stack. The CI/CD gate blocks any vulnerable build from merging, full stop. The engineer assigned gets everything they need. No triage queue. No back-and-forth with security. No deploy until it's resolved.
Auto-generated PRs
Stack-aware patches
CI/CD gate enforcement
Engineer assignment
GitHub Actions
GitLab CI
// STEP 04 — RETEST
Verified closed. Not just marked closed.
After every fix merges, Vortex re-executes the original exploit chain against the patched build. Not a checkbox. A real adversarial rerun against the same attack vector, on the same target. If the vulnerability is gone, it's confirmed. If it regressed, your team knows before production does. Closed means closed.
Exploit chain rerun
Vector confirmation
Regression detection
Auto-triggered on merge
Signed proof record
// STEP 05 — PROVE
Your audit report used to take a quarter. Now it takes one click.
Every closed loop generates a timestamped proof record, automatically mapped to SOC 2 Type II, NIST 800-53, ISO 27001, PCI DSS, and CMMC. Continuous evidence collection means you're always ready for an audit, not scrambling for one. The pentest your compliance framework requires is now the same pentest that runs on every deploy.
SOC 2 Type II
NIST 800-53
ISO 27001
PCI DSS
CMMC
Continuous audit trail
Real-time
evidence collection







.png)



 AWS
AWS