DevSecOps & CI/CD Security
Automated security testing that fits in your pipeline. Not on top of it.
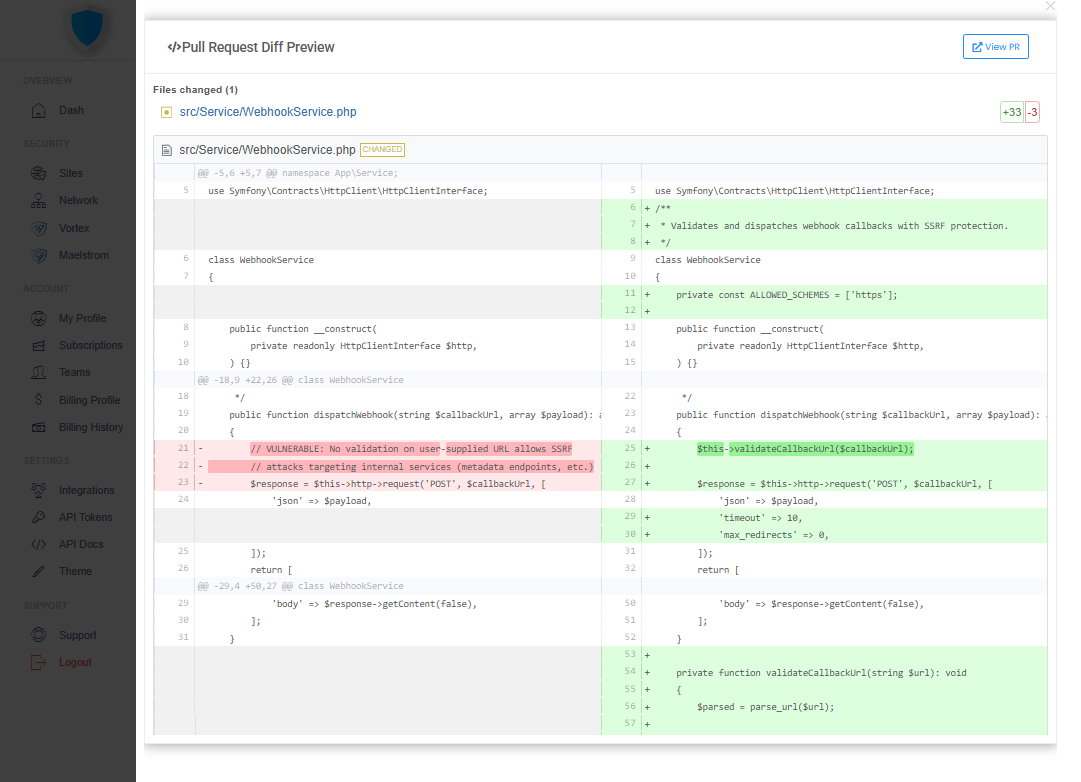
Vortex runs DAST on every commit, PR, and deploy — automatically. Findings go straight to your developers. Fixes ship as pull requests. No new process. No security backlog. Just security that works the way your team already does.
CREST certified. · Trusted by BiteData, NCOG, Hyacinth, and others. · Works with GitHub, GitLab, Bitbucket.