How It Works
Deploy once. Test continuously. Validate everything.
Vortex operates inside your network — not from the outside looking in. That's what makes findings defensible: the agent sees your network the same way an attacker inside it would.
STEP 01 — DEPLOY
Up and running in minutes. Nothing to maintain.
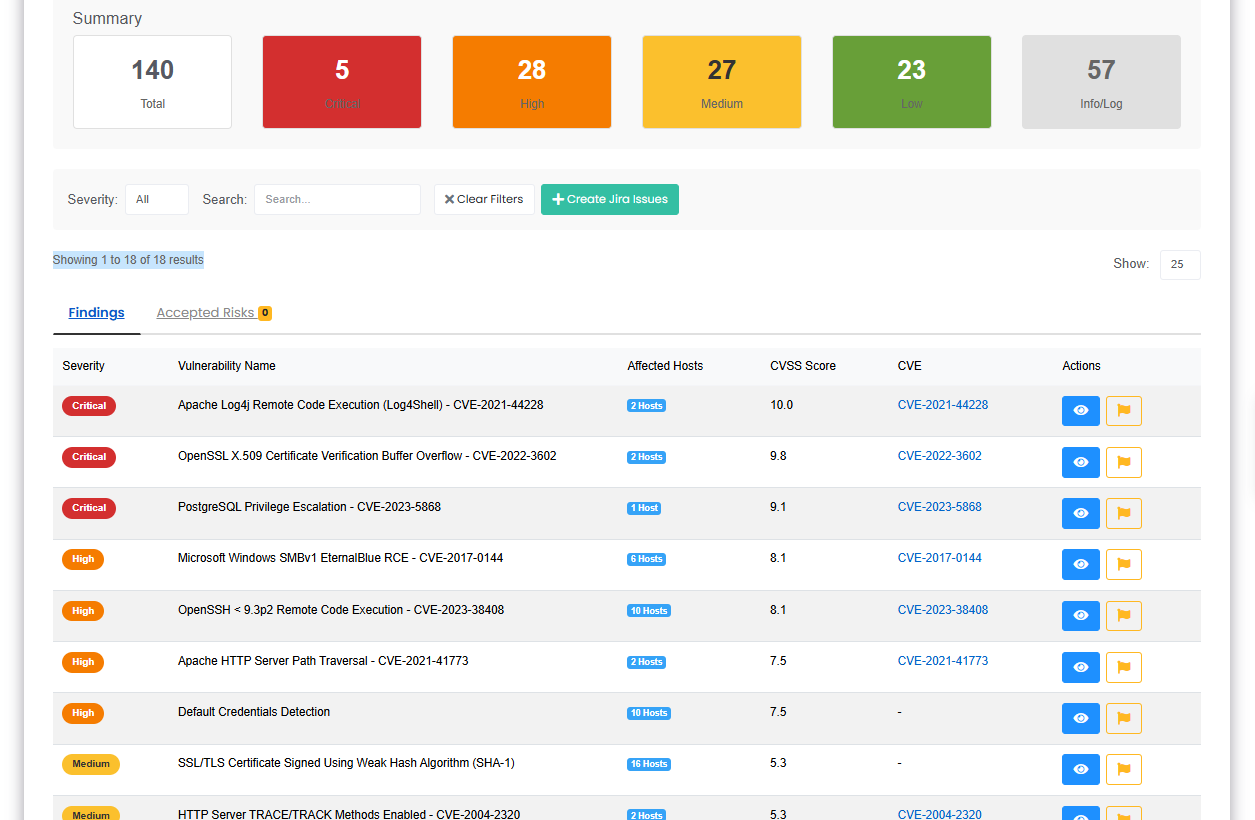
STEP 02 — TEST
Continuous black-box testing across your entire attack surface.
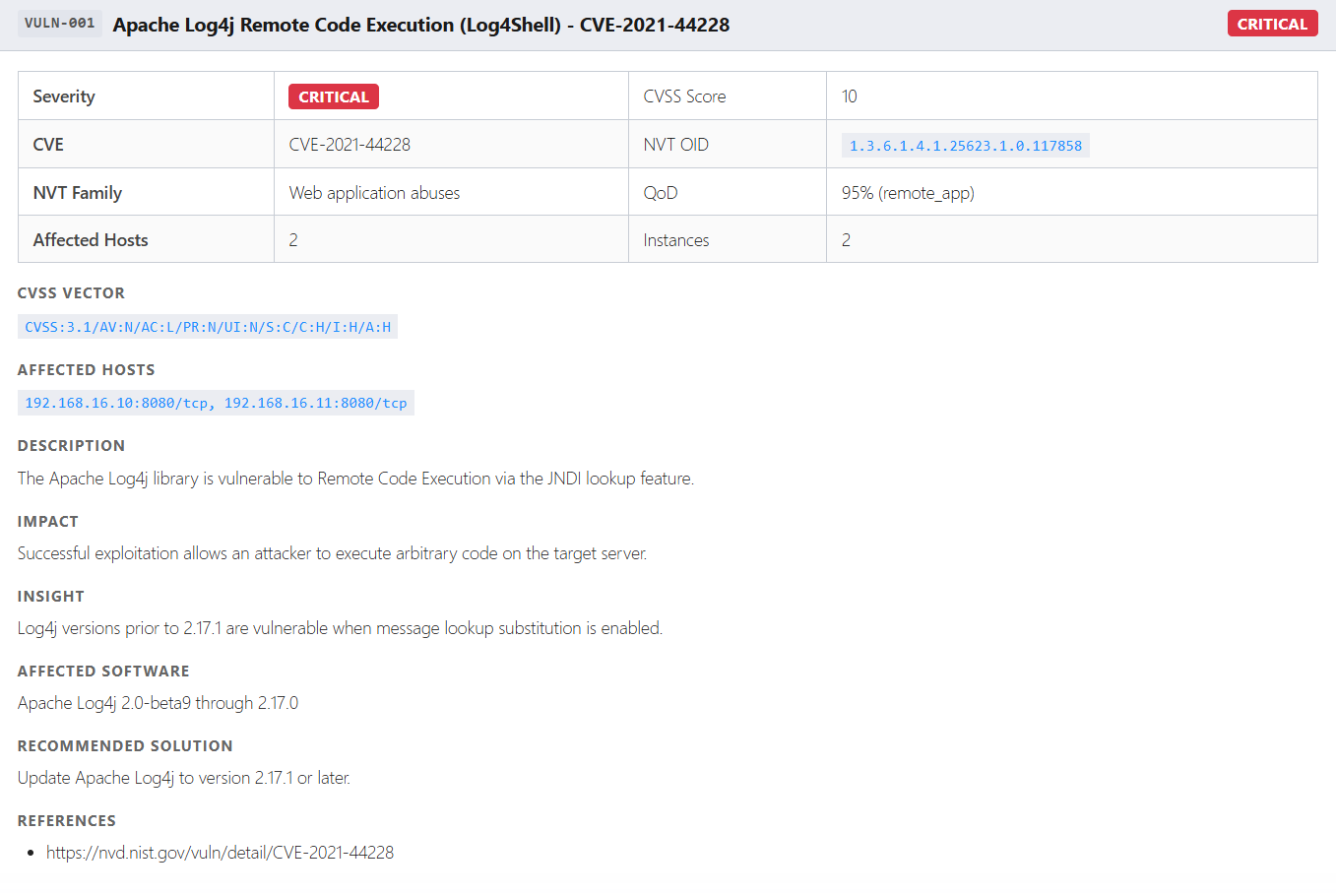
STEP 03 — VALIDATE & REMEDIATE
Only confirmed, network-reachable findings reach your team.