Methodology
The same techniques. Running continuously.
Vortex follows the same four-phase approach a professional penetration tester uses — reconnaissance, vulnerability scanning, exploitation and verification, and reporting. The difference is it runs this workflow automatically, on every change, without a scheduling call or a statement of work.
Vortex maps your attack surface before testing begins — endpoints, authentication flows, API routes, and user-facing components. The map updates on every scan. New endpoints introduced in the latest deployment are in scope for the next run. Nothing goes untested because it was added after the last engagement.
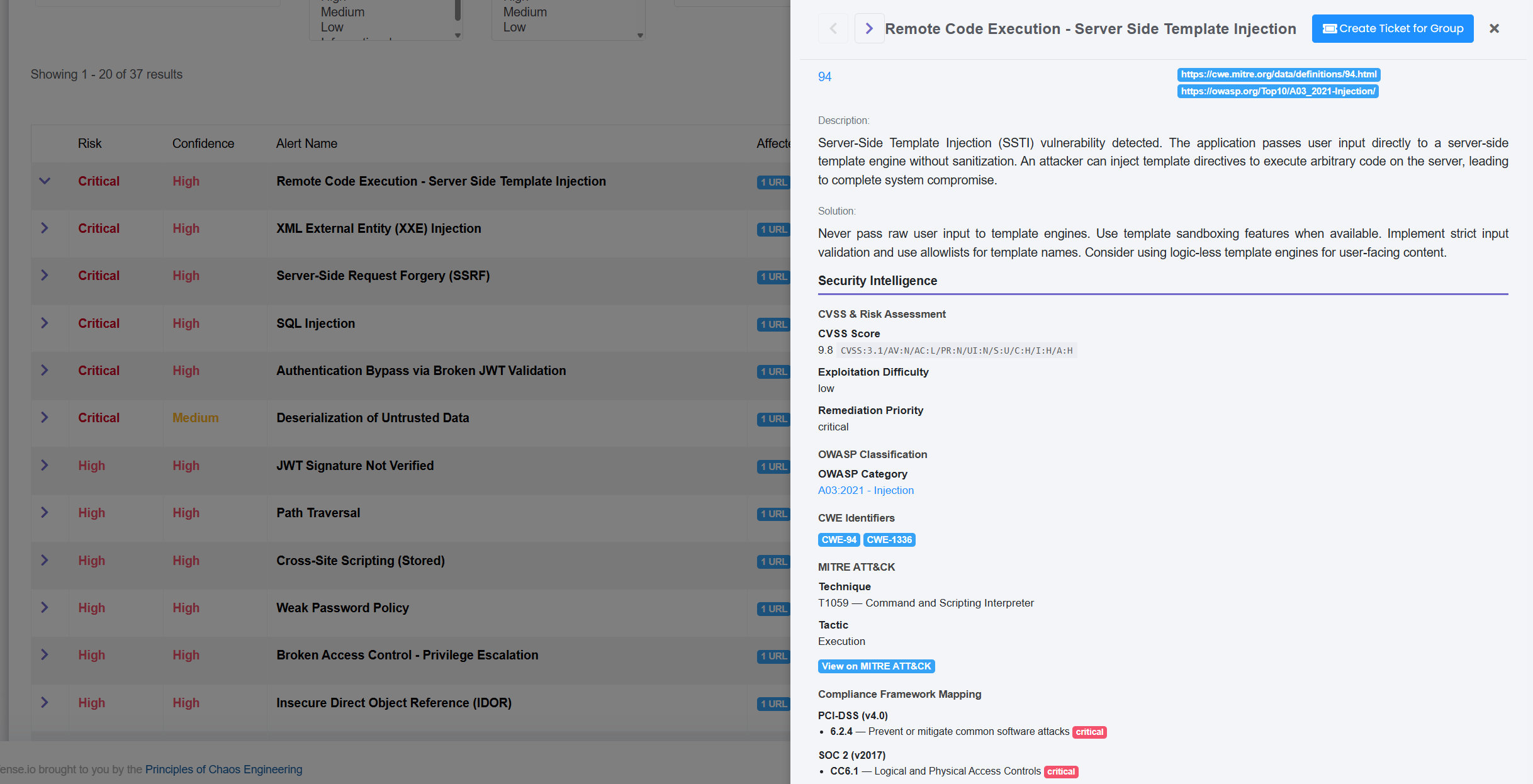
Vortex runs a coordinated battery of 20+ specialized tools simultaneously — covering injection attacks, authentication flaws, broken access controls, server-side vulnerabilities, and modern API attack classes.
Every potential finding is validated with a real exploit attempt. SQL injection findings are validated by demonstrating data extraction is possible. Authentication bypass findings are validated by confirming unauthorized access can be gained. XSS findings are validated by executing the injected payload. If the exploit succeeds, the finding is confirmed. If it fails, it's suppressed. Your team never sees unvalidated findings.
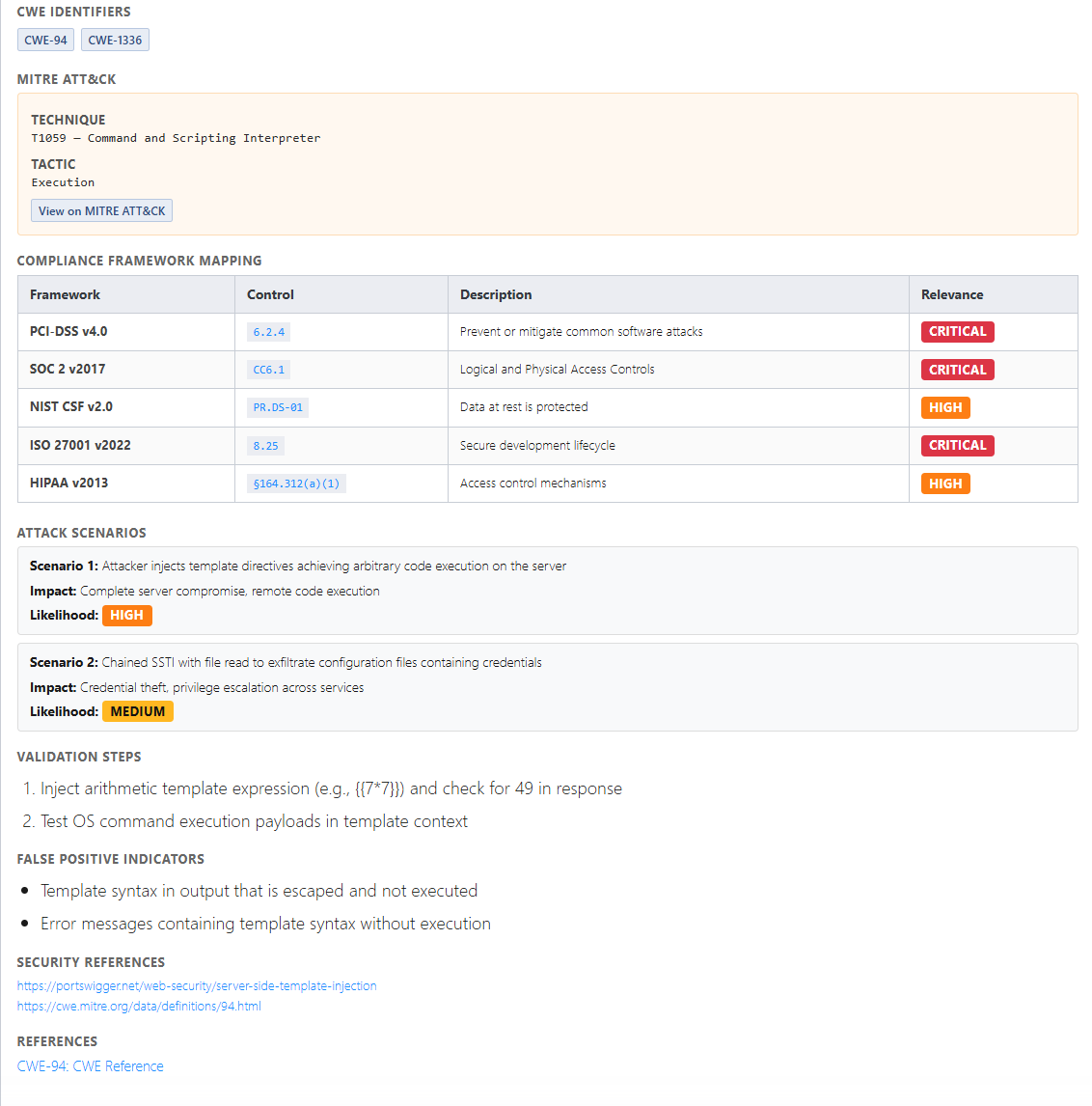
Every confirmed finding comes with a complete evidence package: the vulnerability, the exploit payload used, proof of access, the CVSS score, the MITRE ATT&CK mapping, the OWASP category, and the compliance control mappings. Remediation guidance is specific to your environment and technology stack — not a link to a CVE page. Available in real time, not weeks after the engagement closes.
See full technical detail →