The Evidence Package
Everything your auditor needs. Attached to every finding.
Every finding Vortex surfaces includes a complete evidence package. Not a summary. Not a CVE reference. The full record — from discovery to remediation to retested closure. Here's exactly what's in it.
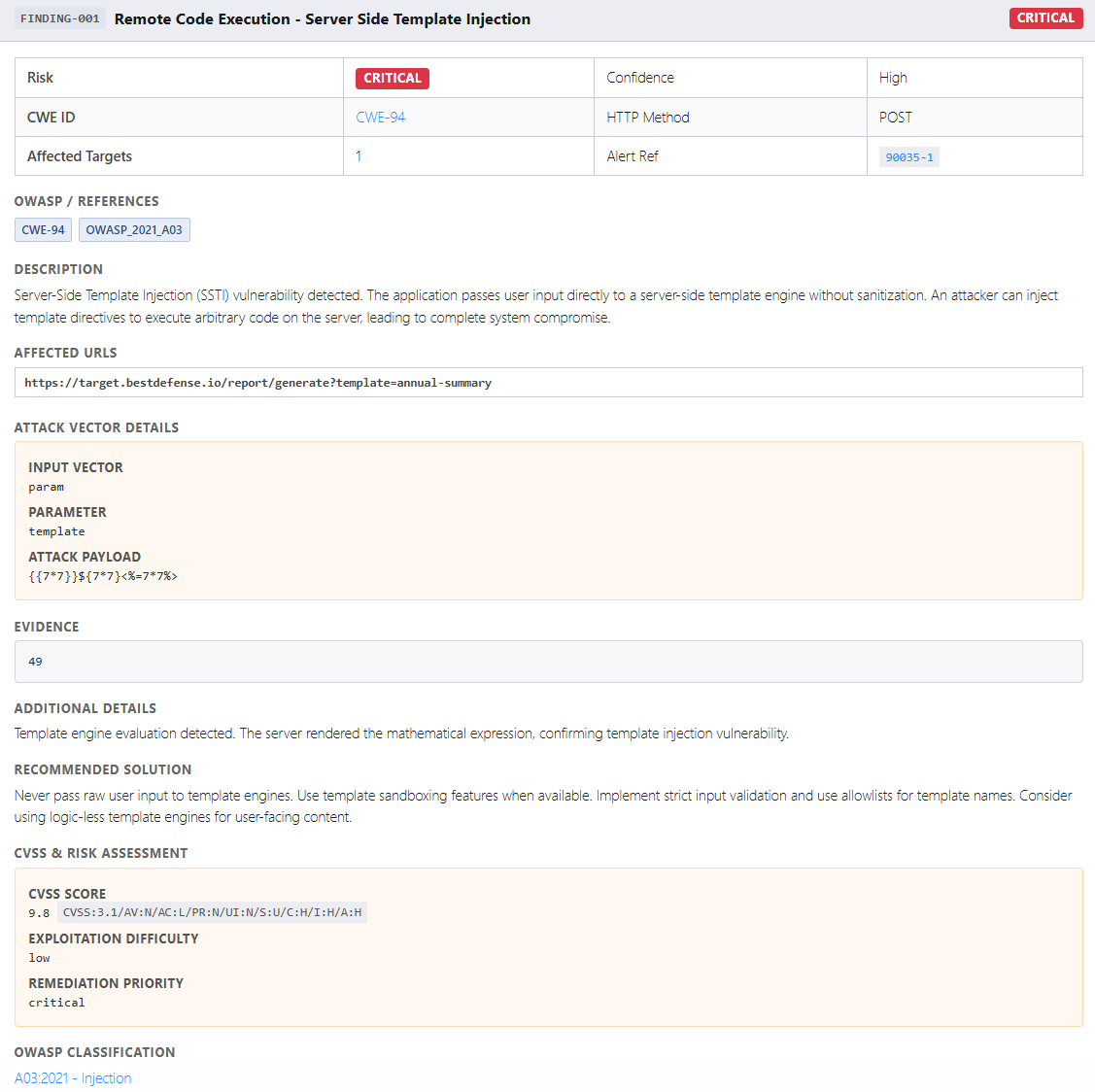
| Field | What It Contains |
|---|---|
| Vulnerability detail | Name, risk level (Critical / High / Medium / Low / Informational), affected endpoint, HTTP method, parameter |
| Exploit evidence | The exact payload used, the response captured, data accessed (if any) — proof the vulnerability was confirmed, not assumed |
| CVSS score & vector | Numeric score + full CVSS 3.1 vector string — the standard scoring format auditors and QSAs recognize |
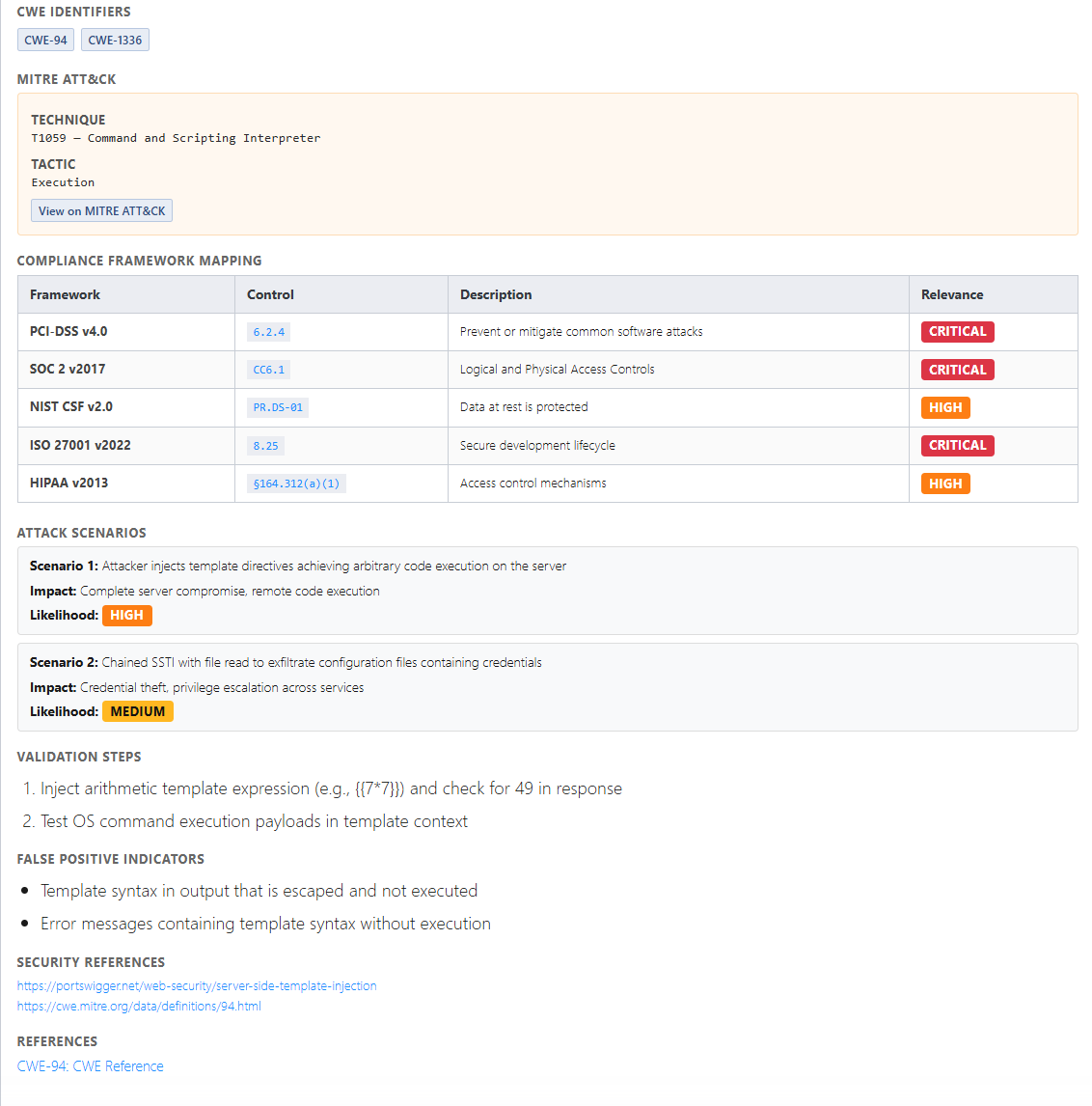
| CWE classification | Common Weakness Enumeration ID with reference link |
| OWASP category | Mapped to OWASP Top 10 category — the framework most web application audits reference |
| MITRE ATT&CK mapping | Tactic, technique ID, and technique name — maps the finding to the attacker behavior framework |
| Compliance control mappings | Per-finding control mappings across all seven frameworks — control IDs, descriptions, and relevance ratings |
| Remediation record | Fix type, fix content, timestamp applied, who applied it |
| Retest record | Retest timestamp, retest result (confirmed resolved / persists) |
| Discovery timestamp | ISO 8601 timestamp — every finding is dated to the minute |
| Ticket reference | Linked Jira ticket ID and status — the full workflow trail |
Every field in that table is populated automatically. No manual entry. No post-processing. No formatting for different auditors.
Report generated automatically on test completion. All framework control mappings included by default.